When that they had entry to Protected Wallet ??s system, they manipulated the consumer interface (UI) that clients like copyright workers would see. They replaced a benign JavaScript code with code made to alter the supposed place in the ETH while in the wallet to wallets managed by North Korean operatives. This malicious code would only goal pre
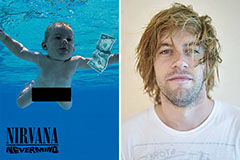 Spencer Elden Then & Now!
Spencer Elden Then & Now! Michael Bower Then & Now!
Michael Bower Then & Now! Alisan Porter Then & Now!
Alisan Porter Then & Now! Marla Sokoloff Then & Now!
Marla Sokoloff Then & Now! Nicki Minaj Then & Now!
Nicki Minaj Then & Now!